In an era where cyber threats are becoming increasingly sophisticated, businesses must rethink their approach to cybersecurity. Traditional methods of securing data and communications are no longer sufficient to protect against the evolving landscape of cybercrime.
As organizations strive to safeguard their sensitive information, they must consider innovative solutions that not only enhance security but also improve operational efficiency. One such solution is the use of the TOR network, which offers a unique approach to hosting websites, managing emails, conducting meetings, and storing files. This blog post will explore the benefits of utilizing TOR for business operations and how it can serve as a viable option for enhancing cybersecurity.
Understanding TOR: A Brief Overview
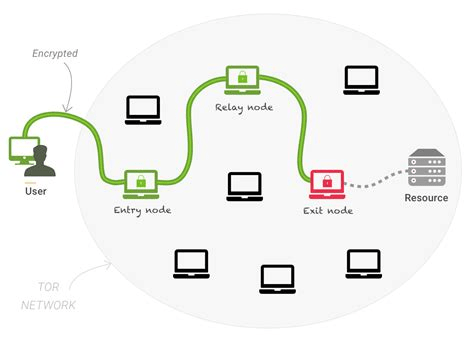
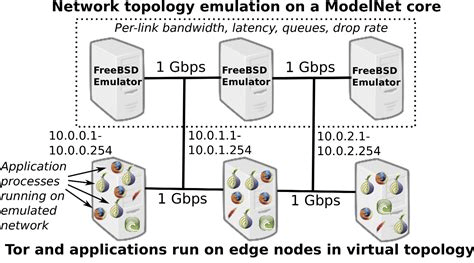
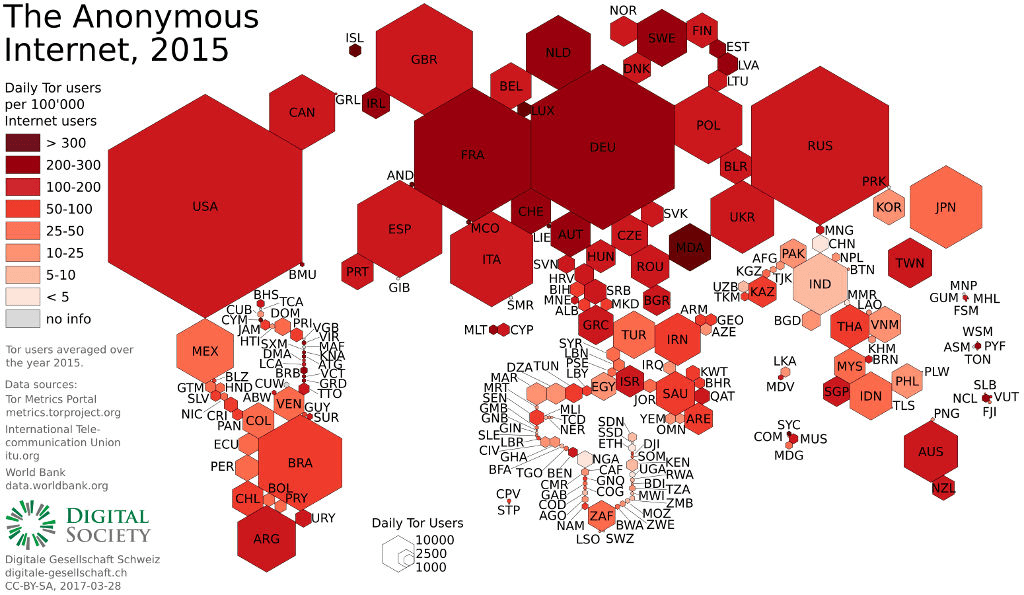
The TOR (The Onion Router) network is a decentralized system designed to provide anonymity and privacy for its users. By routing internet traffic through a series of volunteer-operated servers, TOR obscures the user’s location and usage patterns, making it difficult for third parties to track online activities. Originally developed for military and intelligence purposes, TOR has since gained popularity among privacy advocates, journalists, and everyday users seeking to protect their online identities.
For businesses, TOR presents an opportunity to enhance cybersecurity by providing a secure environment for various operations. By leveraging TOR, organizations can mitigate risks associated with data breaches, unauthorized access, and surveillance.
The Need for Rethinking Cybersecurity
The increasing frequency and severity of cyberattacks have prompted businesses to reassess their cybersecurity strategies. According to a report by Cybersecurity Ventures, cybercrime is projected to cost the world $10.5 trillion annually by 2025. This staggering figure underscores the urgency for organizations to adopt more robust security measures.
Traditional cybersecurity approaches, such as firewalls and antivirus software, are no longer sufficient to combat advanced threats. Cybercriminals are employing sophisticated techniques, including phishing, ransomware, and social engineering, to exploit vulnerabilities in systems. As a result, businesses must explore alternative solutions that prioritize privacy and security.
Hosting Websites on TOR
One of the most compelling applications of TOR for businesses is hosting websites on the TOR network. By creating a .onion site, organizations can provide a secure platform for their customers while maintaining anonymity. This is particularly beneficial for businesses that handle sensitive information, such as financial institutions, healthcare providers, and legal firms.
Benefits of Hosting on TOR
- Enhanced Security: Hosting a website on TOR significantly reduces the risk of DDoS attacks and other cyber threats. Since .onion sites are not indexed by traditional search engines, they are less likely to be targeted by malicious actors.
- Anonymity: Businesses can operate without revealing their physical location or IP address, protecting them from potential attacks and legal scrutiny.
- Access Control: Organizations can implement strict access controls, ensuring that only authorized users can access sensitive information.
- User Privacy: Customers can browse and interact with the website without fear of being tracked, fostering trust and loyalty. Secure Communication with TOR
In addition to hosting websites, businesses can utilize TOR for secure communication. Email and messaging applications that operate over the TOR network provide an added layer of security, ensuring that sensitive information remains confidential.
Using OnionShare for Secure File Sharing
OnionShare is an open-source tool that allows users to share files securely over the TOR network. By creating a temporary .onion address, users can share files without exposing their identity or compromising the security of the data.
Benefits of Using OnionShare
- End-to-End Encryption: Files shared through OnionShare are encrypted, ensuring that only the intended recipient can access the information.
- No Centralized Server: Unlike traditional file-sharing services, OnionShare does not rely on centralized servers, reducing the risk of data breaches.
- Anonymity: Users can share files without revealing their identity, protecting both the sender and recipient from potential threats. Conducting Meetings Securely
With the rise of remote work, businesses must prioritize secure communication during virtual meetings. TOR can facilitate secure video conferencing and messaging, allowing organizations to conduct meetings without the risk of eavesdropping.
Benefits of Secure Meetings on TOR
- Privacy: Meetings conducted over the TOR network are less susceptible to interception, ensuring that sensitive discussions remain confidential.
- Reduced Risk of Surveillance: By using TOR, businesses can protect themselves from government surveillance and unauthorized access.
- Secure Collaboration: Teams can collaborate on projects without the fear of their communications being compromised. Challenges and Considerations
While the benefits of using TOR for business operations are significant, organizations must also consider the challenges associated with its implementation.
- Performance: The TOR network can be slower than traditional internet connections due to the multiple layers of encryption and routing. Businesses must weigh the trade-off between security and performance.
- User Education: Employees must be educated on how to use TOR effectively and securely. This includes understanding the importance of maintaining anonymity and recognizing potential threats.
- Legal Implications: Depending on the jurisdiction, using TOR may raise legal concerns. Businesses must ensure compliance with local laws and regulations regarding data privacy and internet usage. Consulting with legal experts can help navigate these complexities.
- Integration with Existing Systems: Transitioning to a TOR-based system may require significant changes to existing IT infrastructure. Organizations must assess their current systems and determine how best to integrate TOR without disrupting operations. Implementing TOR in Your Business Strategy
To successfully incorporate TOR into your business operations, consider the following steps:
- Conduct a Risk Assessment: Evaluate your current cybersecurity posture and identify vulnerabilities that TOR could address. This assessment will help you understand the potential benefits and challenges of implementing TOR.
- Develop a Comprehensive Plan: Create a detailed plan outlining how TOR will be integrated into your business operations. This plan should include timelines, resource allocation, and training requirements for employees.
- Invest in Training: Educate your team on the importance of cybersecurity and how to use TOR effectively. Training should cover best practices for maintaining anonymity, recognizing phishing attempts, and securely sharing information.
- Pilot Program: Before fully committing to TOR, consider running a pilot program with a small team or department. This will allow you to test the system, identify any issues, and gather feedback before a wider rollout.
- Monitor and Adapt: Continuously monitor the effectiveness of your TOR implementation and be prepared to adapt your strategy as needed. Cybersecurity is an ever-evolving field, and staying informed about new threats and technologies is crucial. Conclusion
As cyber threats continue to evolve, businesses must rethink their approach to cybersecurity. The TOR network offers a unique solution that enhances security, privacy, and operational efficiency. By hosting websites, managing emails, conducting meetings, and sharing files through TOR, organizations can significantly reduce their risk of cyberattacks and protect sensitive information.
While there are challenges associated with implementing TOR, the potential benefits far outweigh the drawbacks. By investing in training, conducting thorough assessments, and developing a comprehensive plan, businesses can successfully integrate TOR into their operations and create a more secure environment for their employees and customers.
In a world where data breaches and cybercrime are becoming increasingly common, embracing innovative solutions like TOR is not just a strategic advantage; it is a necessity. By prioritizing cybersecurity and exploring new technologies, businesses can safeguard their future and thrive in an increasingly digital landscape.
As we move forward, it is essential for organizations to remain vigilant and proactive in their cybersecurity efforts. The time to rethink how we approach cybersecurity is now, and TOR may just be the key to unlocking a safer, more secure business environment.
Leave a comment